
Engine Yard Kontainers Is Now Generally Available
We are delighted to announce that the Engine Yard Kontainers is now LIVE. Engine Yard Kontainers (EYK), is a fully managed container-based infrastructure to run

We are delighted to announce that the Engine Yard Kontainers is now LIVE. Engine Yard Kontainers (EYK), is a fully managed container-based infrastructure to run

According to a 2020 report from DataDog, nearly 90% of containers are run using container orchestration tools. What’s more interesting is that in 2018, only

Balancing Developer Productivity andSoftware Quality


Docker is one of the fastest-growing technologies in 2020, and with good reason. Dockeris a piece of software for performing virtualization. Essentially, Docker mimics the

Docker is a software solution for performing virtualization. With so many eyes on this cloud computing technology, it is hard to distinguish between Docker containers

Cloud infrastructure has become elastic, agile, and resource-efficient over the past decade – particularly with containerization and the broad adoption of Docker and Kubernetes.
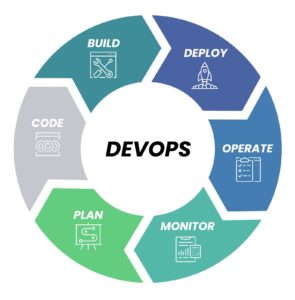
DevOps benefits at a fraction of the cost

Engine Yard has always made it easy for you to deploy your applications to the cloud. Over years, the cloud has evolved. The cloud now

In this age of technology, web applications are everywhere in our lives. There are many hurdles in the application deployment process, and many steps to
ENGINE YARD
A NoOps PaaS for deploying and managing applications on AWS backed with a world-class support offering.
DEVSPACES
DevSpaces is a cloud-based, dockerized development environment that you can get up and running in minutes.
CLOUDFIX
A cloud cost optimization service that automatically scans your AWS account to identify cost savings opportunities and implements user-approved fixes.
SCALEARC
A SQL load balancer that enables you to dramatically scale and improve database performance without any code changes to your application or database.
CODEFIX
A highly scalable, automated code cleanup service that finds and fixes issues automatically so that you can focus on developing new features.
14 day trial. No credit card required.